Is Your Network Security Adequate? Think Again!
 Back on February 7th, NBC reported on potential security risks at the Olympic Games. There was a lot of controversy about the article itself, but, accurate or a hoax, IT security doesn’t get the attention it should in small businesses. More and more organizations, large and small, are being audited either by regulatory agencies or by existing or potential clients. Years back, news was about virus attacks, followed by malware; today we’re regularly hearing about hacking. Everyone wants to know their data is secure.
Back on February 7th, NBC reported on potential security risks at the Olympic Games. There was a lot of controversy about the article itself, but, accurate or a hoax, IT security doesn’t get the attention it should in small businesses. More and more organizations, large and small, are being audited either by regulatory agencies or by existing or potential clients. Years back, news was about virus attacks, followed by malware; today we’re regularly hearing about hacking. Everyone wants to know their data is secure.
Data security is critical to ANP’s network management practices. We protect data by leveraging “organizational wide” network security management best practices. Having a firewall, unique passwords, and anti-virus programs might feel adequate, but times have been changing. It’s critical to look closely not only at the IT infrastructure within your offices, but also at equipment owned by your staff and maybe even your vendors.
As I’m writing this blog, I’m sitting at home on my personal computer connected to the office. There are lots of options for remote workers these days, but there are also network security risks that need to be mitigated if you have a mobile or remote work force. Let’s touch on a few.
Home computers are usually vulnerable to viruses and malware due to lack of ongoing management and “the kiddie factor.” Microsoft and other vendors do an adequate job of providing anti-virus and malware support for home computers, but only if the tools are leveraged and leveraged correctly. If virus or malware activity infects your home computer and it is connected to the office network, you’ve just introduced a “back door” network security risk. Could your organization be vulnerable to a home-based worker?
What about mobile devices like smart phones and tablets? Apple iPhones and iPads are acknowledged to be natively more secure than Android devices. Do your employees use both for connecting to the office? You may limit their use to email, but do you also allow them into the office? Onto the office wireless network? ANP regularly performs Network Assessments for prospective clients. It’s surprising to see how few companies segment their networks, restricting mobile device traffic solely to guest wireless networks. There are also data security risks associated with email on mobile devices. Just last week we completed an assessment for a company that was sending unsecured email to mobile devices, risking precious client information being shared with the outside world.
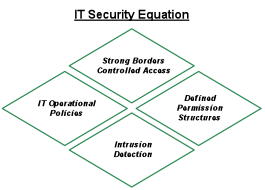
What about inside your offices? Firewalls are designed to protect your network, and they do, but they are only one piece of the network security equation. Some of my clients leverage Intrusion Detection software to further analyze traffic passing through their firewall. Though this software can be pricey, understanding the data these systems produce reinforces the need for a strong network security policy and operational discipline.
In a 30-day period, I’ve seen “locked down” firewalls allow attempts at accessing servers from almost 20 different countries around the world. That’s why network security is about a “system” of hardware, software, and operational procedures tightly woven to protect the organization and its sensitive data.
Here are a few questions to discuss with your IT staff or outsourced provider. Your answers will determine the next steps needed to establish appropriate levels of network and data security in your business:
- How old is our Firewall and how current is its Operating System?
- What is our Server and Workstation Patch status and update process?
- Do we have any Windows XP computers in our network?
- What is our password management strategy?
- How do we control and manage access to sensitive information on our Servers?
- Do we have a guest wireless network for employee smart phones and guest traffic?
- When is the last time we had an outside network security Assessment?

