What is Multi-factor Authentication and Why You Need it Now
If there’s one security feature you must absolutely implement right away it’s multi-factor authentication (MFA). Yes, you could make a case that your firewall, anti-virus, or user management system is the number one security measure. It’s true that you need some of those before you can even get to MFA, but nobody can debate the effectiveness of MFA.
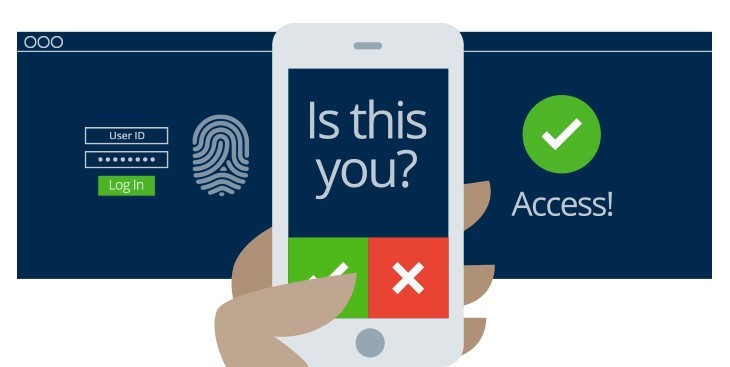
Multi-factor authentication, sometimes referred as two-factor authentication (2FA), essentially provides you with 2 or more credentials to authenticate your identity. The first is usually a password and the additional credential usually consists of something you have on you physically, making it much more difficult for a hacker to steal.
By adding another step in the authentication process, hackers can no longer break into your account with just your email and password. If they obtain your password through a phishing attack or via brute-force, MFA will require that they have that second credential, making the authentication process even more secure.
Multi-factor authentication can help prevent some of the most common and successful types of cyber attacks, including:
- Ransomware
- Phishing
- Spear phishing
- Keyloggers
- Credential stuffing
- Brute force and reverse brute force attacks
- Man-in-the-middle (MITM) attacks
You’re probably using MFA is several areas of your life but don't realize it. Most banks and financial institutions now require MFA to access personal information. You may use your thumb print to access your online banking account, or enter a random code sent to you to access your investment portfolio. Even those personal security questions are a form of multi-factor authentication, though the industry is trending away from it because they too can be compromised through a little social media research.
Today more common authentication techniques include:
- Randomly generated codes sent to your phone
- A USB key generator that you plug into a computer port or cell phone that functions to the code sent to your phone, except it’s encrypted
- A push notification sent to an app on your phone
- Your fingerprint, facial recognition or other bio-recognition techniques
- Retina or iris scanning
In the past we have gotten push back from some users who think MFA is a major inconvenience to their workday. But the truth of the matter is that it’s the way of the world today. If you’re not using MFA then your business could be at risk, and once you start using it, you'll realize that it's actually not a hassle after all.
As a business owner or IT manager ask yourself this: if you’re using MFA in other areas of your life – to protect a single credit card for example - why wouldn’t you implement the same standards to protect your business?
When you consider the cost and consequences of a data breach, the extra step to keep your business protected is worth it. Think about all of the information that a hacker could expose if your business was compromised -- your employees’ social security numbers, all of your client’s banking information, your intellectual property and much more.
Multi-factor authentication has proven to be a critical layer of protection that most businesses are making it a requirement today. At ANP we highly recommend MFA to all of our clients.
- Does the security of your business keep you up at night?
- Are you doing everything you can to protect your business?
- Are you interested in testing out multi-factor authentication for your business?
ANP has a wide range of managed security services to keep your business protected. Contact us today to learn more about how you can greatly enhance your business security with ANP for a small monthly fee.

